How is the registration and login function implemented?
The implementation of registration and login functions typically involves several key components and steps. Here’s a basic overview of how it’s done:
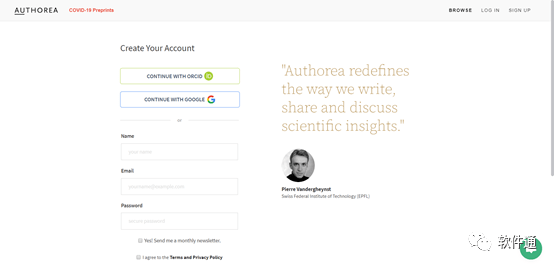
1、User Registration:
The user is prompted to provide necessary information such as username, password, email, etc.
The information is then sent to the server for processing.
The server validates the input data (e.g., checking for uniqueness of username or email, password strength, etc.).
If the data is valid, it is stored in a secure database for future authentication.
2、User Login:
The user is prompted to enter their credentials (username or email, password).
This information is sent to the server for verification.
The server queries the database using the provided credentials.
If a match is found, the server generates a session token or cookie which is sent back to the user’s device.
The user’s device stores this token/cookie, and it is used to identify the user on subsequent requests.
3、Session Management:
Once a user is authenticated, a session is created on the server to track the user’s activity.
The session token/cookie is used to maintain the user’s authenticated status across multiple requests.
If the token/cookie is lost or expires, the user will need to re-authenticate.
4、Security Measures:
To ensure security, several measures are taken during the registration and login process, including encryption of sensitive data, hashing and salting of passwords, and protection against common attacks like SQL injection or brute force attacks.
Additionally, two-factor authentication, email verification, and other security features can be implemented for enhanced security.
In summary, the registration and login functions are implemented by collecting user information during registration, validating and storing it securely, and then verifying the information during login to grant access to the system or application.